Agent Client Assignment
You cannot use agents immediately after they have been installed. For security reasons, you must determine the clients in which the individual agents can be used and the rights that they should have.
Object class: System object
Object type/Short form: HSTA
Once the agents are installed in your system and you have created the clients, you must then establish the connection between agents and clients and define which rights each agent will have on which client.
You can grant agents the necessary rights individually on their Authorization Page, but if you are dealing with many agents, this is very time-consuming. In this case a faster alternative is using the Agent/Client Assignment object (HSTA), where you collect agents and define an authorization policy that you assign to all of them in bulk. The HSTA object then enters the rights specified in the authorization policy in the individual agents.
HSTA objects can be created in system client 0000 only.
An HSTA object definition is made up of the following pages:
- Standard pages that are always available, no matter what type of object you are defining:
- The Agent Authorization Policy page described here.
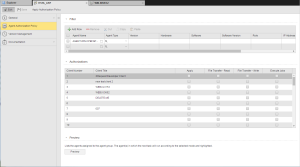
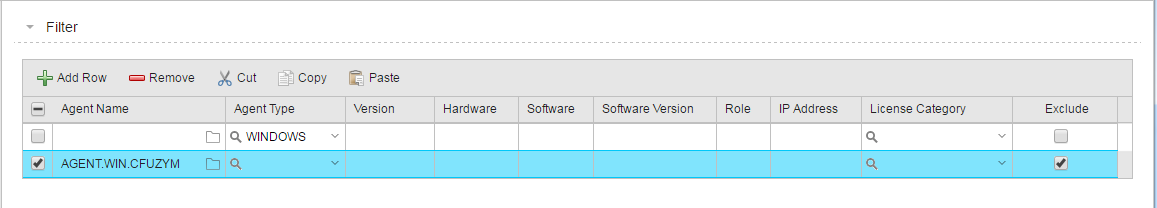
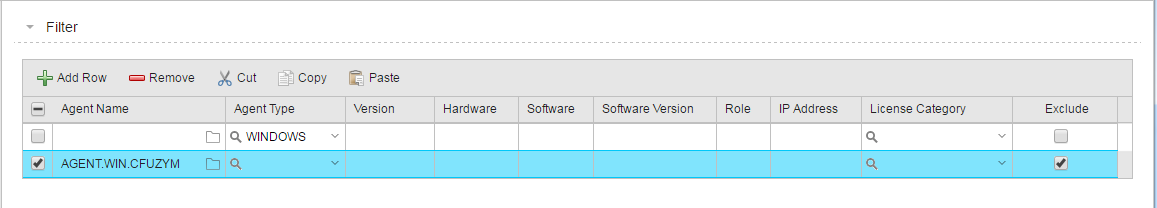
- In the Filter section, create the list of agents to which you will apply the authorization policy in bulk.
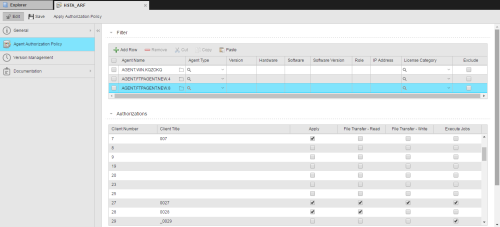
- The Authorizations section provides the list of all the available agents in your system. Specify here the individual rights the agents should have (or not) on the clients.
- In the Preview section, check the client/agent assignment you have just defined.
- Apply the authorization policy.
- Activate the HSTA object
For performance reasons, rights are not assigned every time an agent starts but only when it starts for the first time.
 To Collect Agents in the Filter Section
To Collect Agents in the Filter Section
-
Click the folder icon on the Agent name cell to open the Agent dialog, where you select the agent to include in the list.
| Element |
Description |
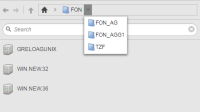
| Folder menu bar |
This allows you to scroll through the folder structure of your system. Click the arrow next to the home icon to open it and select the folder you need. The agents contained in it are displayed in the hit list below.
Navigate through the folder structure using the arrows.
|
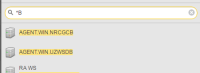
| Quick search field |
Enter a search string here to quickly find tasks in the hit list. You can use the following wildcard characters:
- * as placeholder for any number of characters
- ? as placeholder for exactly one character.
|
- Click OK to insert the agent in the Filter table.
-
Use the table toolbar to add more agents and to arrange them in the list:
| Option |
Description
|
|

|
Inserts a new row at the bottom of the table
|
|

|
Deletes the row |
|

|
Removes the entry from the list and pastes it to the clipboard. Click Paste to add it to the bottom of the table. |
|

|
Duplicates the entry. Click Paste to add it to the bottom of the table. |

|
|

|
Activates all rows in the table. |
-
Activate the Exclude checkbox if you want this agent to be excluded from this authorization policy.
 Example
Example
In the example below you grant all Windows agents certain rights on a number of clients with just one exception: AGENT.WIN.CFUZYM, which is also a Windows agent, will have no access to those clients:
 To Assign Agents to Clients and the Corresponding Rights in the Authorizations Section
To Assign Agents to Clients and the Corresponding Rights in the Authorizations Section
The Client Number and Client Title columns are not editable; they provide the number and title(if available) of the client as specified upon creation.
-
Specify the rights you want to grant the agents in the selected client:
| Right |
Description |
| File Transfer - Read |
The client can transfer (send) files. |
| File Transfer - Write |
The client can receive transferred files. |
| Execute Jobs |
The client can start jobs. |
-
Activate the Apply checkbox to grant the selected rights to the agents in the Filter list.
Please note that you can also activate this checkbox if no rights have been specified for a client.
 Example:
Example:
The three agents depicted in this screenshot are assigned to clients 7, 27 and 28.
- On client 27 they have full rights.
- On client 28 they can only receive transferred files.
- Although the are assigned to client 7, they cannot perform any of the actions associated to these rights.
 To Check the Client/Agent Assignment
To Check the Client/Agent Assignment
Before applying the rights policy on clients to the collected agents you can check whether your definition is correct.
Click the Preview button at the bottom of this page to see the list of agents to which you are about to grant rights. This does not trigger agent assignment, it simply displays the effects that the agent assignment would have with this HSTA object.
You can save and preview your definitions or only preview them. In any case, make sure that you save them before approving the policy.
 To Apply the Authorization Policy
To Apply the Authorization Policy
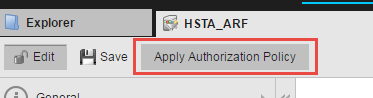
For the settings you have defined in a HSTA object to take effect, you must do the following:
-
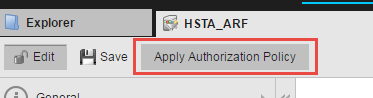
Click the Apply Authorization Policy button on the toolbar:
-
Switch to the Administration Perspective and open the Agent Authorization Policies page. Here you must activate the HSTA object.
The order of objects in the Active list is relevant! If two object contain contradictory definitions, the most recent one will be applied.
![]() To Collect Agents in the Filter Section
To Collect Agents in the Filter Section
![]() To Assign Agents to Clients and the Corresponding Rights in the Authorizations Section
To Assign Agents to Clients and the Corresponding Rights in the Authorizations Section
![]() To Check the Client/Agent Assignment
To Check the Client/Agent Assignment
![]() To Apply the Authorization Policy
To Apply the Authorization Policy